The Facts About Data Security Services Uncovered
and modern technology solutions give skilled assistance as well as service for your network, so you can concentrate on what your company does ideal. The service benefits of managed solutions in mix with the cash you can conserve make it a wise solution for firms of any kind of size. is when a company contracts out certain IT operates to a third-party carrier, described as a Managed Provider or.
The objective is to either function as an IT group for a business that has little or no inner abilities or to support an experienced IT group by taking a few of the everyday tasks off their plate. Can took care of services lower cost? The answer is of course. It can likewise make your IT expenditures much more foreseeable.
An in-house IT group, on the various other hand, includes much more frequent as well as unanticipated expenses that can swiftly drain your budget. Networks included a whole lot of devices that needs to be preserved as well as occasionally repaired or changed. upkeep as well as repair services as component of the contract, so a fix that may cost you hundreds of bucks out of pocket is taken in by the company.
Excitement About Data Security Services

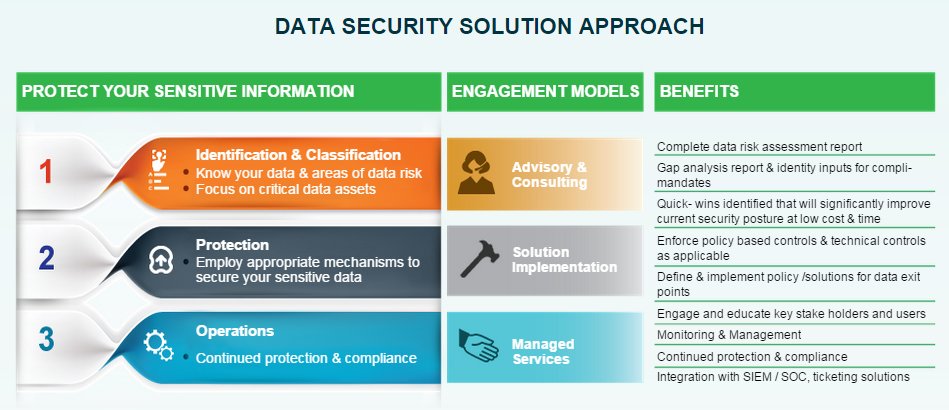
Getting access to the very best cybersecurity options and technologies is a vital asset as well as incentive to start working with a Managed Security Solutions Supplier. An also gives independent cyber-security guidance; this isn't the instance for suppliers of equipment and tools. Among the main advantages of functioning with a Managed Safety And Security Services Carrier is the broad cyber-security expertise it uses, something that several companies do not have internal.
The certified workers of excellent MSSPs are always conscious of growths in the industry as well as in modern-day cyber dangers. Organizations that place their count on in an are usually more efficient at shielding their very own organizations than when they depend on their own safety groups alone. Obviously, this doesn't alter the truth that both groups have to make proper plans concerning just how they connect with one another.
An MSSP can: Day in, day out, have to handle many safety and security informs stemming from numerous protection tools used within the firm. Simply put, alerts commonly fall short in their function: they're either not functional or do not consist of info that might be utilized to take activity. This type of alert fatigue increases the possibility that actual cyber dangers will certainly go undetected.
How Data Security Services can Save You Time, Stress, and Money.
Numerous cyber-security solutions trigger assimilation issues when trading data, causing ineffective as well as inadequate data silos. MSSPs normally have integrated innovation solutions that completely concentrate on action-oriented alerts. So if your sends you signals, these are seldom repetitive or pointless. data security services. A lot of MSSPs make use of the technology of all types and also dimensions that in-house experts have official statement actually integrated in time for organizations.
As well as if you require to downsize at a later time, you can. react promptly. The price tag connected with maintaining an in-house IT team is a large one, which's why you commonly see groups that are understaffed, overworked and incapable to obtain whatever done because of an absence of time as well as resources.
Training also one added staff member for your IT division expenses countless bucks, as well as there is never a guarantee that they'll even remain with the firm. An MSP soaks up the expense of training, as well as you'll never have to fret about your IT specialists leaping ship. Scaling networks takes considerable coordination, workforce and also brand-new devices.
A Virtual CIO is a solution some MSPs supply that supplies analysis, strategy and also a detailed prepare for the company's technology - data security services.
The Data Security Services PDFs
The idea of linking people as well as data from anywhere at any kind of time result in the development of cloud computing in the 1960s. It came along with numerous safety and security dangers such as information breach, information loss, hijacking of accounts, insecure APIs, rejection of service and insider threats which paved method for the principle of cloud safety and security.
Disaster recovery plans can also be carried out conveniently when all the info is handled in one location. With the best cloud safety and security procedures in place, people can safely access information and also applications within the cloud no issue where they are or what gadget they utilize. Cloud computing enables organizations to expand exponentially, reduce technology prices as well as utilize nimble methods in order to fulfill the competitors.
As the cloud system is based on the utility, you need to pay just to the service provider simply for what you make use of. Cloud computer enables multiple users to accessibility as well as share data while recording at the exact same time which makes it easy for the employees that work offshore or in the house to service the data promptly and also quickly via any web-enabled solutions.


 A managing representative is usually appointed to take control of the role of running the whole structure,
A managing representative is usually appointed to take control of the role of running the whole structure,